AD/LDAP Authentication with Multiple Domains
Introduction
Important
This is only applicable to on-premise deployments.
This guide will show you the steps to configure Active Directory or LDAP for multiple domains.
Prerequisites
Important
This feature has been designed to only work a flat Active Directory structure.
- Appspace Core user credentials with Portal Administrator role.
- Active Directory enabled with Administrator-level credentials.
Configuring Active Directory Authentication with Multiple Domains
Important
You MUST setup the Active Directory in your server with an Administrator-level account BEFORE going through this authentication process.
Step 1
Click the profile (settings) icon on the top-right corner of the toolbar and select System tab.

Step 2
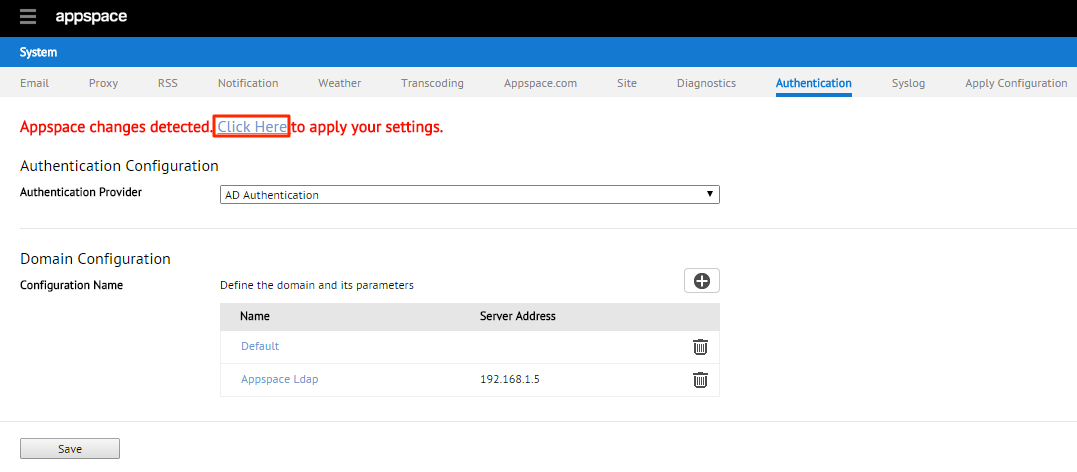
Click the Authentication tab and choose AD Authentication from the drop-down menu. To add a Domain click on the + symbol.

Step 3
Complete the relevant details in the AD Authentication Parameters section, including Server Address, Port, Username, Password, Default Account and Base DN. Click on Validate Connection to verify connection is successful to the AD.

Warning
Please create an Administrator-level account (in this case, Superuser) in your Active Directory BEFORE proceeding with this step to avoid Appspace system lock-outs
Note
The credentials shown in the screenshot are provided only as an example. For more information on obtaining Active Directory credentials, please consult your organization’s IT Department or personnel. For Windows Server 2008 onwards would require the full CN name of users.
Ports: 389 (Non-SSL) / 636 (SSL).
Server Address: The AD server’s IP should never be used when deploying with SSL.
Step 4
To validate the configuration fill in the Text Field box with the username of any user that belongs to the Domain and click Submit. A successful validation will display a property table of the user.

Step 5
Once connection is validated proceed to the Property Mapping section to map the Source Property of the user to the Target Property available from the drop down list. You can also set the Automatic User Creation to Enable or Disable.

Sample default values:
- FirstName: givenname
- LastName: sn
- Email: mail
- Username: samaccountname
The Enable option will allow users who do not have an existing Appspace login to log in and it will automatically create a login for the user.
The Disable option will allow Administrator to manually Import users however Property mapping must be setup prior to this.
Step 7
The following status message will be displayed at the top of the page. Select the Click Here link to apply the settings you have made.
Step 8
A new Apply Configuration subtab will be displayed. Complete the Appspace installation server’s username and password credentials in the relevant sections and click Apply

Step 9
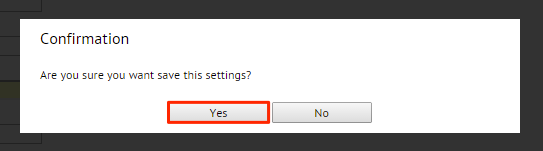
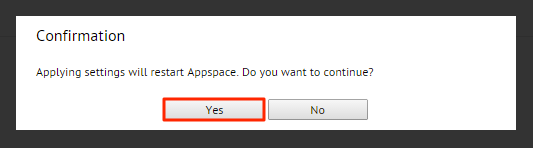
Click Yes in the Confirmation dialog box.
Note
In the event of an error message, please verify your authentication settings and credentials. Press the OK button to try again.
Step 10
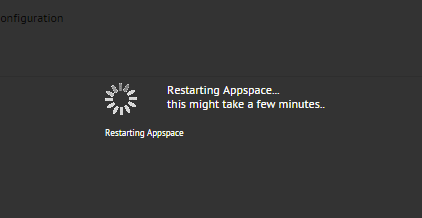
If all the details and credentials were entered correctly, allow a few moments of inactivity while the system restarts itself.
Step 11
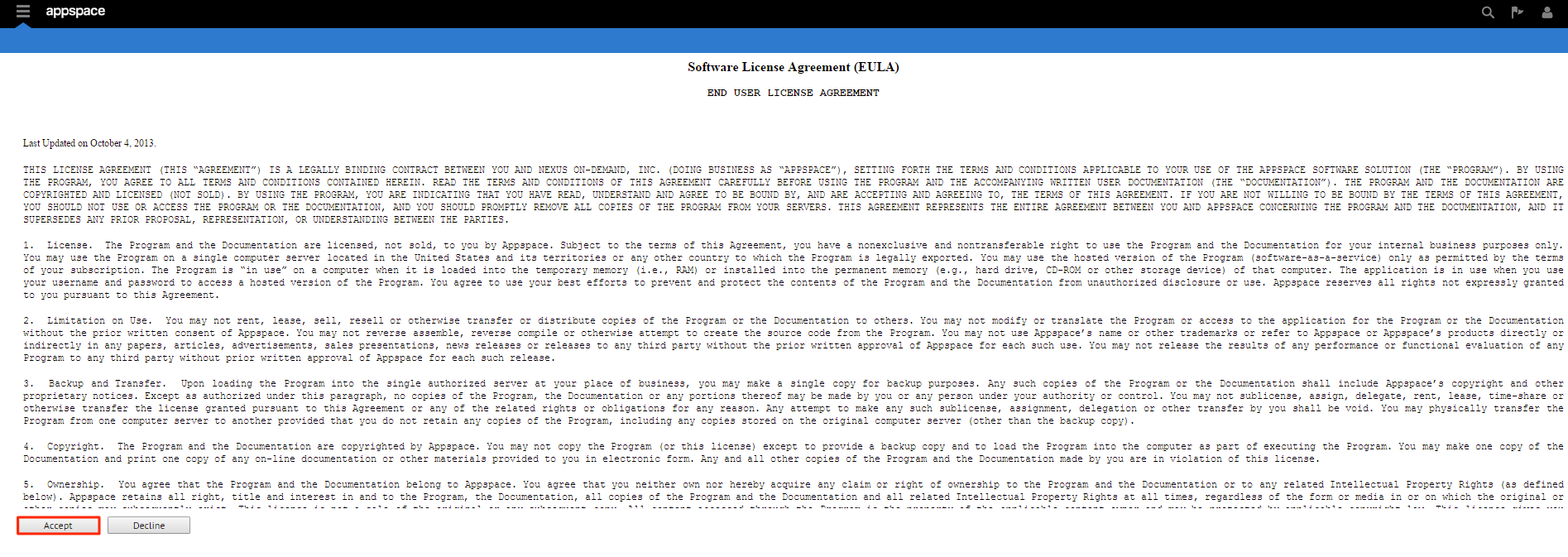
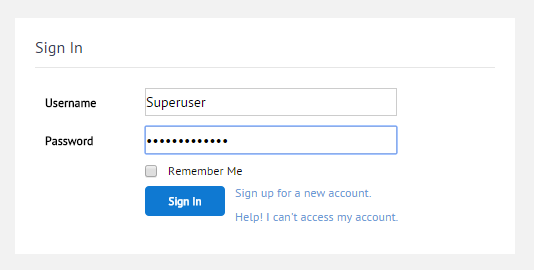
Once Appspace has restarted, verify that the AD authentication has been processed by logging out of your Appspace account and logging in again using the AD username (Superuser) and password credentials. If Automatic Creation is enabled it will automatically create the user and upon successful creation user will be presented with the EULA. Click Accept to proceed.
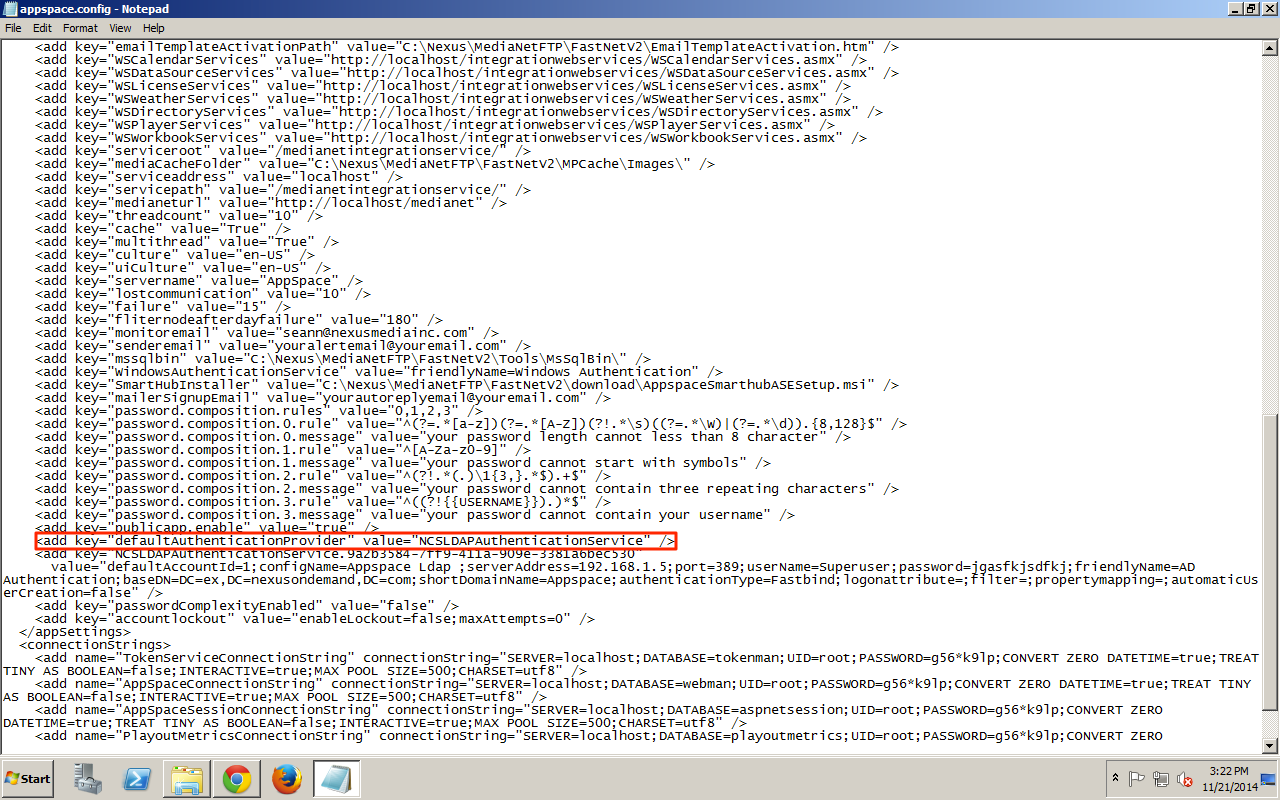
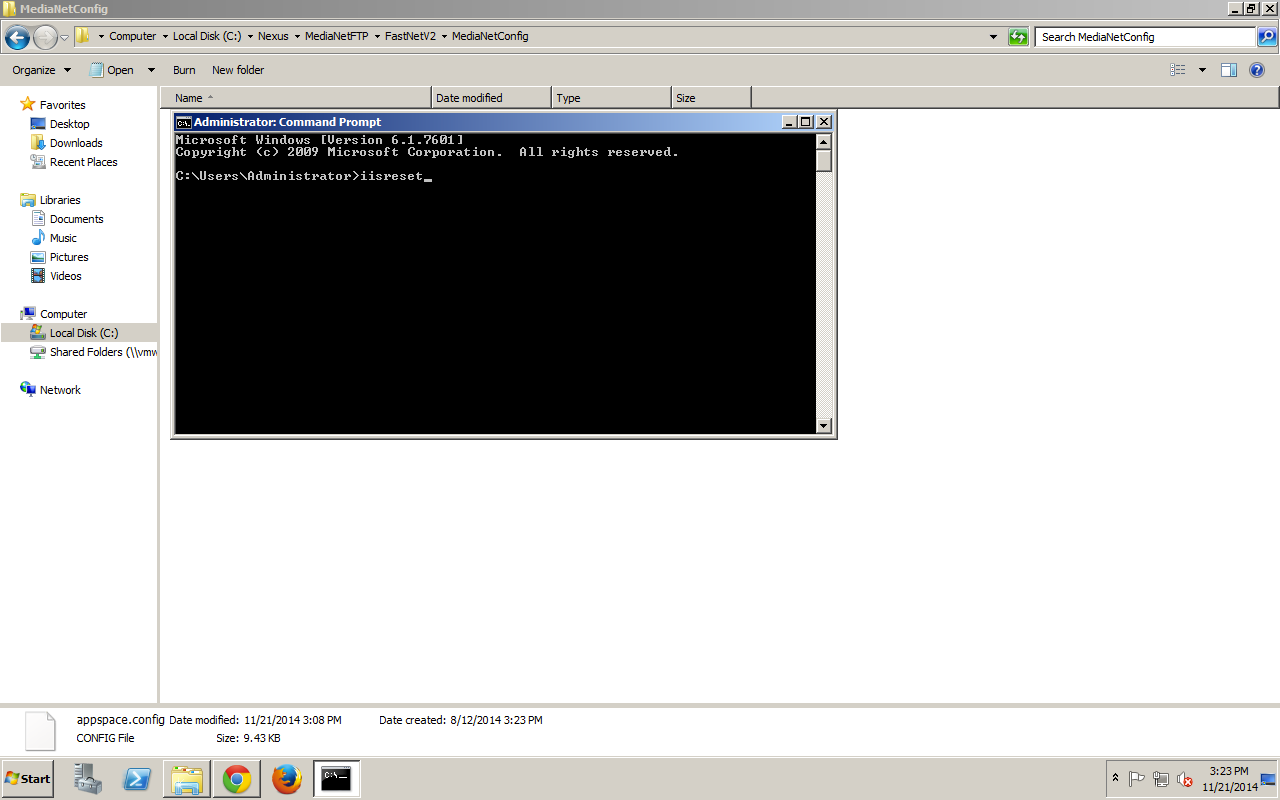
Rolling Back Active Directory Authentication
In some instances (such as an On-Premise installation), you may need to roll back AD Authentication and revert back to Appspace Authentication. The following guide explains the necessary steps to perform this task.
Step 1
On your Windows server computer, locate the AppSpace installation folder. Browse to the MediaNetConfig folder (by default it is located at C:/Nexus/MediaNetFTP/FastNetV2/MediaNetConfig).